Authena.xyz
A pluralistic identity verification system that powered 400K+ on-chain proofs
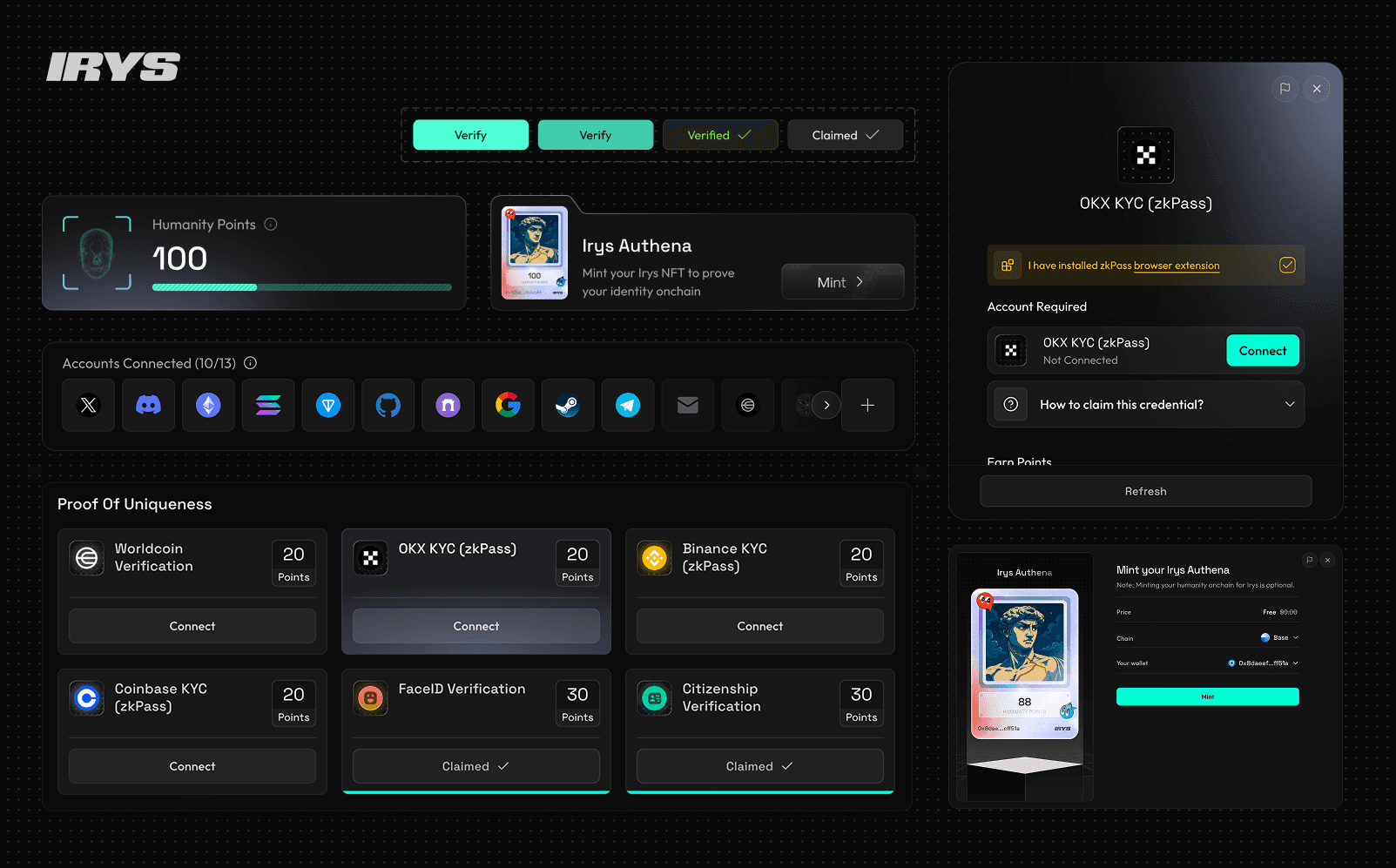
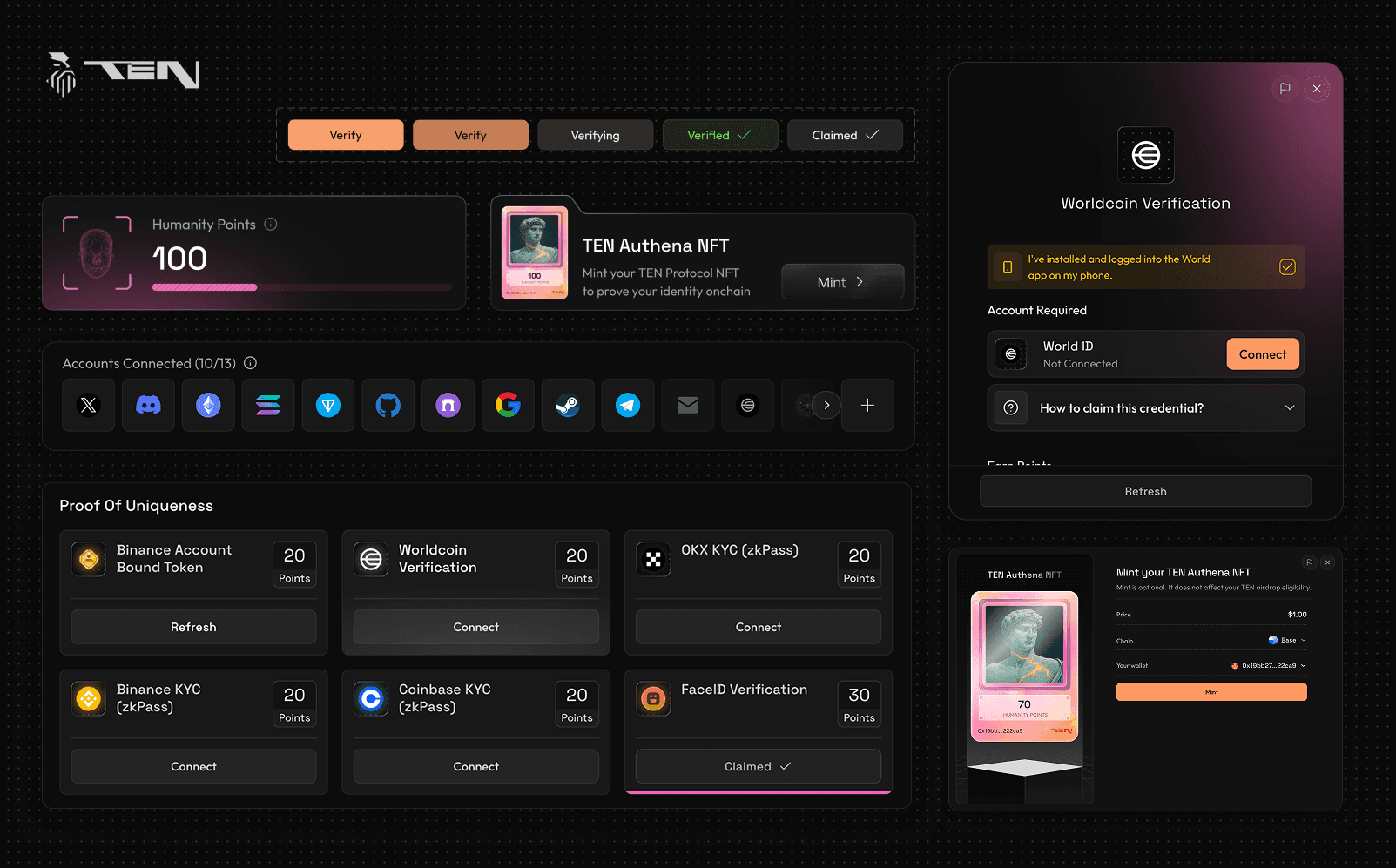
Designed Authena’s credential verification and NFT minting experience from scratch as a white‑label product. Built a reusable design system that let our dev team ship 10+ different protocol configurations without custom design work. The system supports 15+ credential signals (government ID, biometric, social, and on-chain), with protocols choosing their own credentials and point system.
My Role:
Design Lead
Timeline:
~2 Month
Team:
2 Designers, 1 Product Manager
5 other key stake holders across
Business, Marketing and Engineering
Context and Problem:
Why Web3 airdrops needed a pluralistic identity layer?
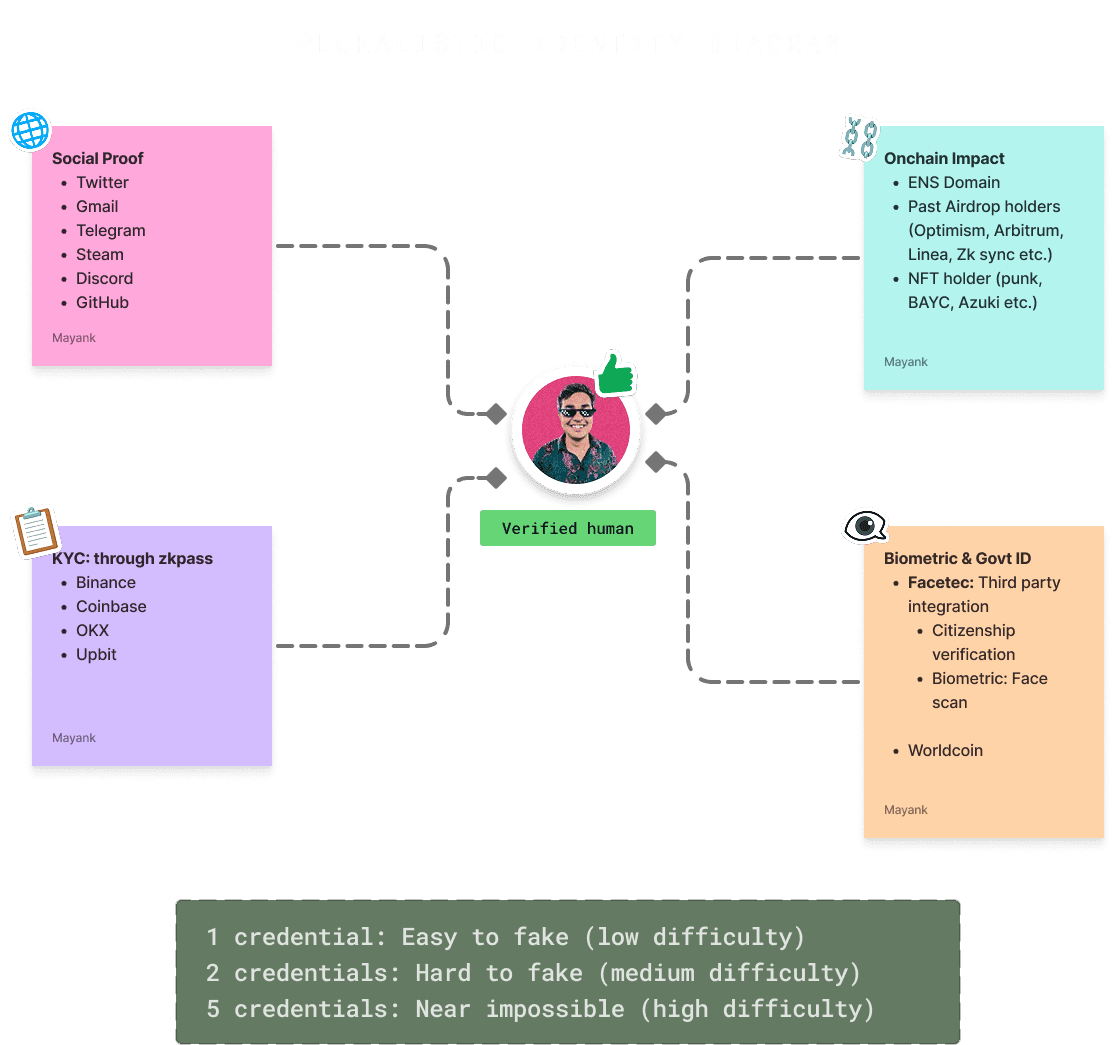
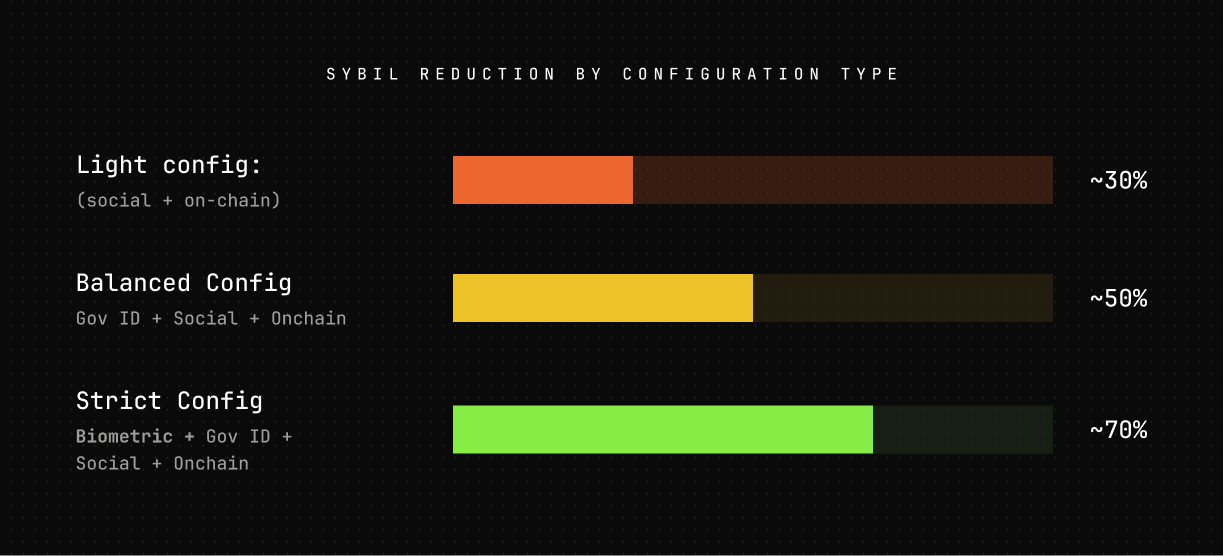
Through research with 15+ Web3 protocol founders, we identified a pattern: Web3 airdrops were hemorrhaging 30-70% of budgets to Sybil attacks. But existing proof-of-humanity solutions (BrightID, Worldcoin) had <5% adoption due to high friction, privacy concerns, or inflexibility.
Founders needed two things: flexible verification (different security levels for $100K vs $10M campaigns) and proven case studies before they'd trust any solution.

Design strategy: Instead of one rigid credential, we built a pluralistic system.
Multiple overlapping proofs (social + government + biometric + on-chain). A scammer can fake one signal; faking five is exponentially harder. This became our competitive moat.
Product Role and Constraints:
Role:
Owning Authena end‑to‑end. From first UX concepts to the live verification and NFT minting flows used by 10+ protocols.
Designing a white-label solution with Interaction patterns, visuals and UI components as a core requirement.
What Authena had to do:
Position as a TGE wedge product (short-term revenue) while building toward identity infrastructure (long-term moat)
Support 20+ credential types that protocols could compose based on risk appetite
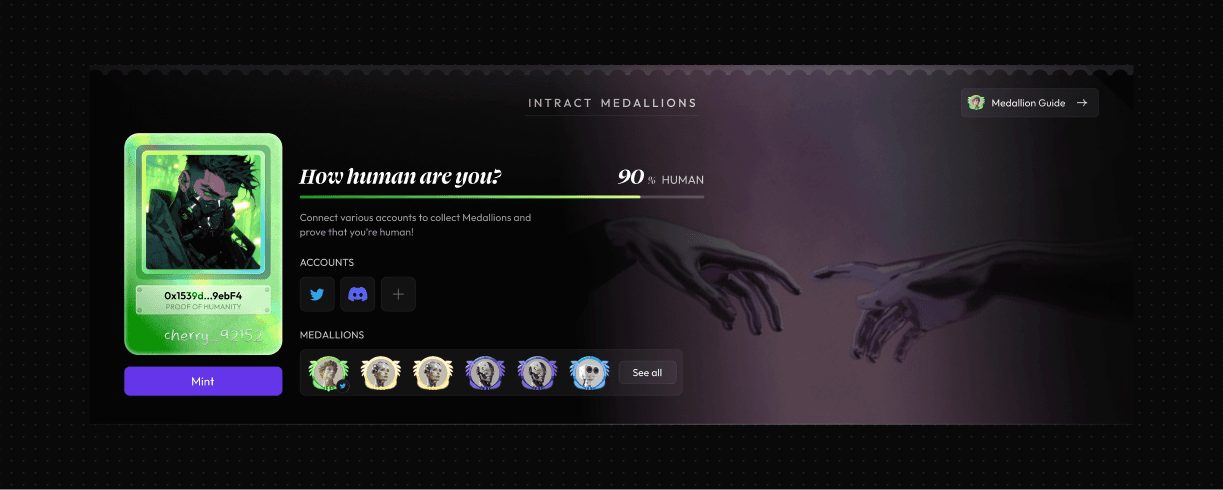
End in an on‑chain NFT mint that serves as portable proof across protocols
Design components
Specific UX Problems and Solutions:
🔴 Problem 1: Heterogenous credentials UI and flow killed the trust
❌ Previous Version: Showed 40%+ drop-off when users hit their 2nd or 3rd credential. Every credential was different, so users didn't trust what would happen next.
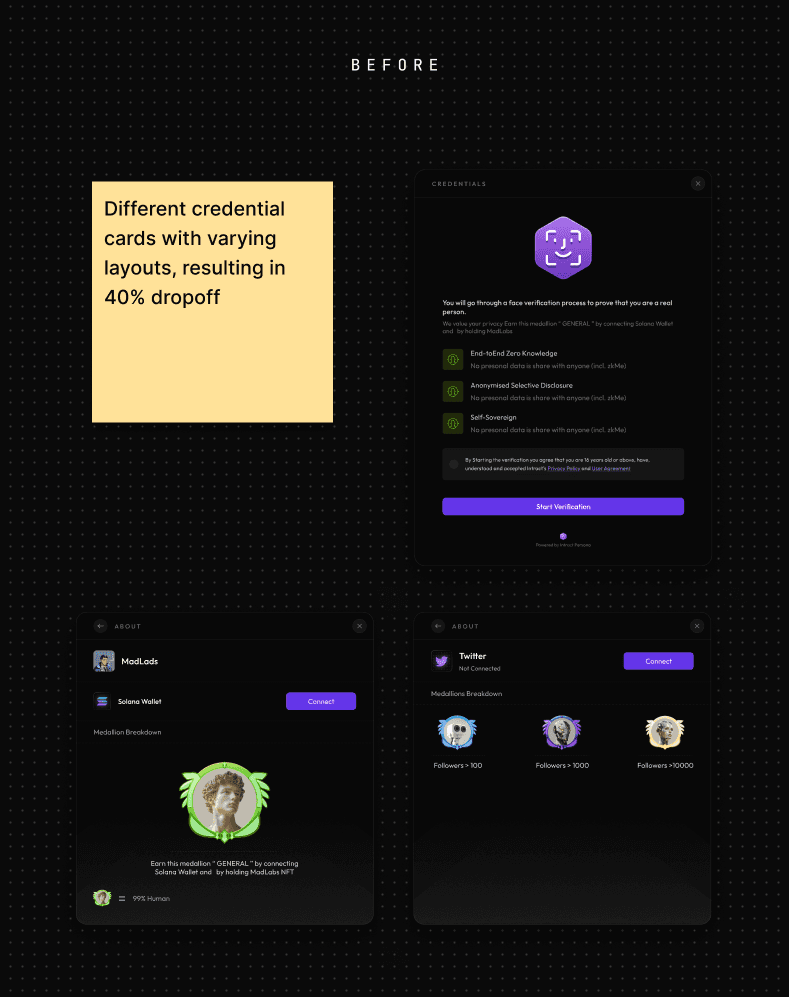
✅ New Approach: Radical consistency across all 15+ credential types. Same card layout, same "Verify" button placement, same loading states, same success confirmation. Users memorized the pattern after 2-3 verifications.
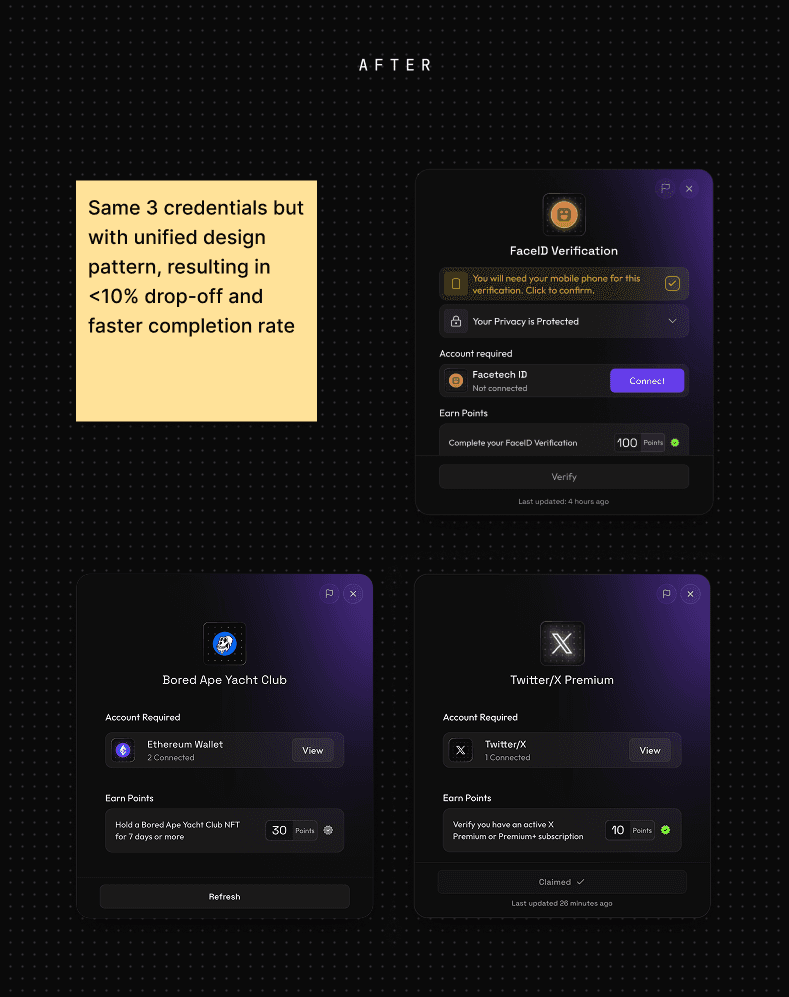
✅ Result: Drop-off rates between credentials decreased to <10%. Consistency > delight in high-stakes verification.
🔴 Problem 2: Variable credential counts broke standard progress patterns

🔴 Problem 3: When to prompt users to mint the NFT?
User testing revealed confusion: "Do I need to mint to be eligible?"
✅ Design decision: Auto-trigger celebratory modal the instant minimum score is hit. Minting is optional (users are already eligible), but the celebration drove 15% more users to mint NFT, creating permanent on-chain records valuable for protocol analytics.

Data and Outcome:
Metric
Sybil reduction
NFTs minted
Protocols shipped
Revenue
Mint conversion
Support rate
Results
30–70% across different credential configs
~400K on‑chain proofs in 12–18 months
10+
$600K ARR ($50K MRR)
75%+ of users reached minimum score minted the NFT
1–2% of users (mostly wallet/gas issues, not UX confusion)
What the data taught us:
Case studies close deals
After our first 3 flagship TGE launches, BD conversion accelerated 3x. Founders trusted proven results over technical whitepapers.
Privacy messaging matters
Adding ZK-proof credentials reduced privacy concern objections from 35% to <10%
Flexibility > perfection
Protocols valued customizable credential mixes over one "perfect" verification flow. The 30-70% range proves different security needs require different approaches.
✅ Result: Different protocols configured different credential mixes, and stricter combinations reduced Sybils more. Points of credentials were adjusted accordingly.
Designing as a White‑Label System:
Locked components
Credential cards, buttons, modals, states. Following same structure across all protocols.
Flexible theming
Logo, Color Scheme, typography adapt to each brand.
Reusable flows
Wallet → credentials → celebration → mint NFT works for all.
✅ Result: New protocol launches by applying the design system + swapping theme/copy. No redesign needed. This is how Authena has supported 10+ concurrent deployments with $50K MRR



Takeaways:
Pluralistic identity was the right bet
Multiple overlapping signals (social + government + biometric) reduce Sybils 30-70% more than singular credentials. This positioning differentiated us from BrightID and Worldcoin.
White-label design systems aren't optional at $50K MRR
We couldn't manually redesign for each protocol and maintain margins. Locked components + flexible theming let us ship 10+ variants without custom design work
Strategic constraints drive better design decisions
Privacy compliance forced ZK-proofs (initially complex) → We simplified with clear messaging. Variable credential counts broke
Authena logo and cta to project